Google Project Zero announced that they have discovered 11 zero-day exploits being actively used to hack Android, Windows, and iOS devices. Hackers have been using ‘malicious websites’ to gain access to sensitive parts of the operating systems.
Project Zero shared that the team discovered seven zero-day exploits in February and October 2020—where “a couple dozen websites” were redirecting vulnerable users to one of two exploit servers. One of the servers was focused on attacking iOS and Windows users, and the other was focused on Android devices.
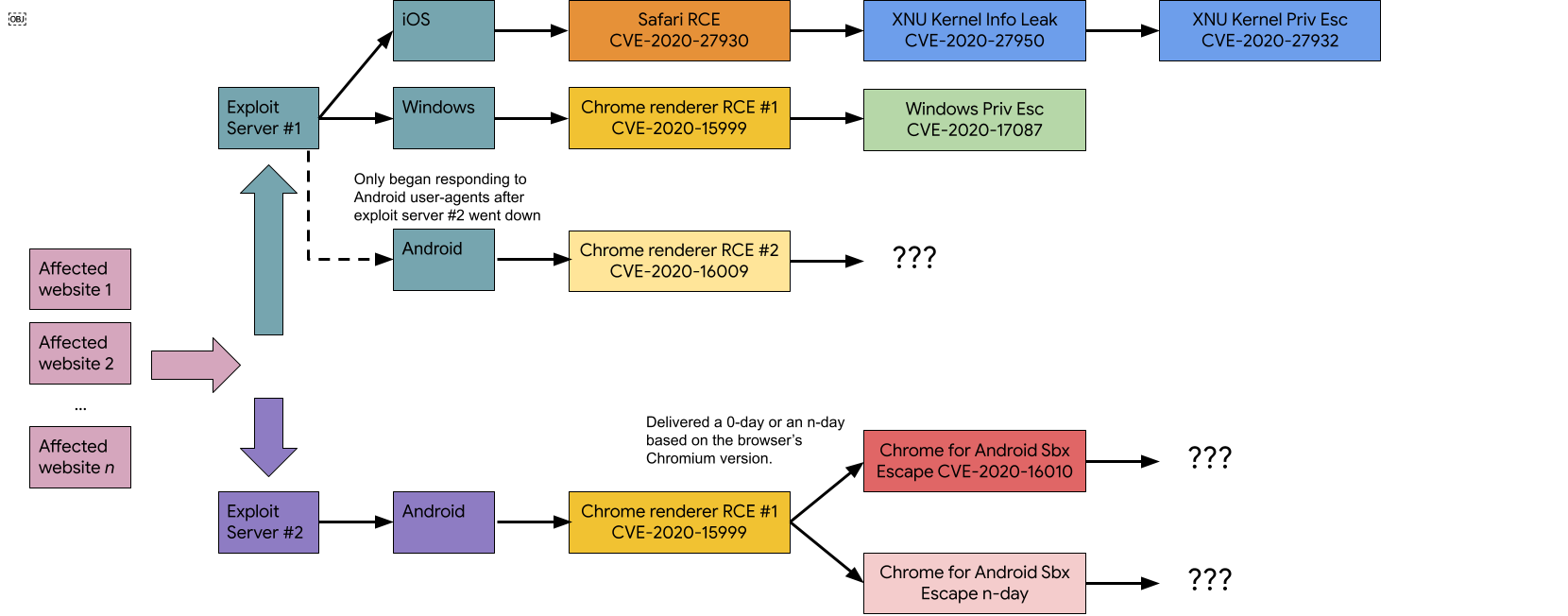
Exploit server #1 initially just responded to iOS and Windows servers with the Safari and Chrome browsers. However, it briefly responded to Android servers after exploit server #2 went down. Exploit server #2 only responded to Android servers with the Chrome browser.
The report mentioned that hackers had “advanced knowledge” of what they were doing as they were able to bypass the security systems of “well-fortified OSes and apps that were fully patched”. They were also able to quickly reopen the breach after Google updated the Chrome engine with a fix.
“We are so thankful to all of the vendors and defensive response teams who worked their own long days to analyse our reports and get patches released and applied,” wrote Project Zero.
You can find more details on the 2020 breach on Google Project Zero’s blog. They’ve also listed the technical details of each of the vulnerabilities and exploits.
Project Zero also published details in December 2020 about a zero-click iOS vulnerability that allowed attackers remote access to victims’ iPhones. It gave hackers total control over their devices, including email, messages, and photos access.
Here’s a reminder that you shouldn’t visit websites that you don’t fully trust. You should also keep the software on your devices up to date to avoid security issues.
[ SOURCE, IMAGE SOURCE ]








