A mysterious strain of malware was found to have infected about 3.25 million Windows-based computers for two years between 2018 and 2020. The database was recently uncovered and and “spotted on the dark web”, as reported by Nordlocker.
“With some help from third-party researchers, we uncovered and analysed a database of stolen data. It’s big—and the victims likely never knew their files had been stolen,” wrote Nordlocker.
What was stolen?
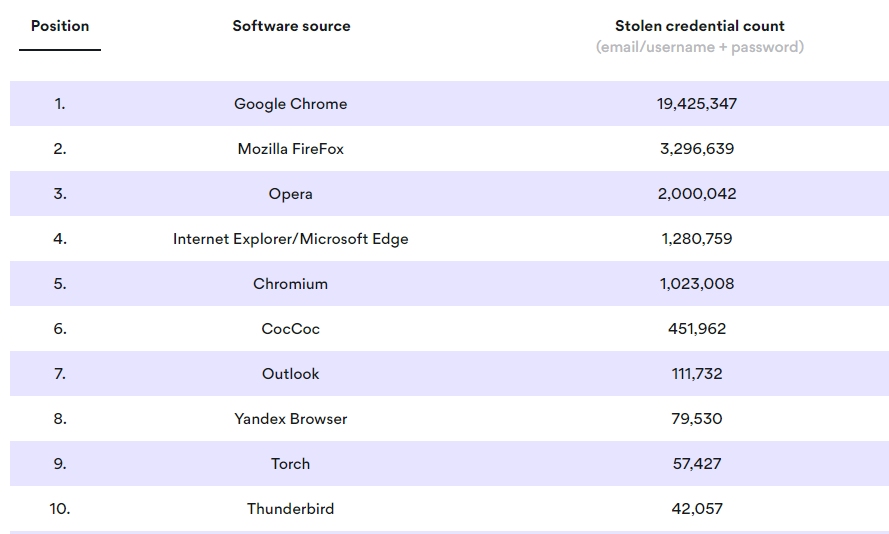
The stolen database included 1.2 TB of files, cookies, and credentials containing usernames and passwords. It had 2 billion cookies which can be used to identify users, their habits and interest. And over 400 million of those cookies were still valid at the time when the database was discovered.
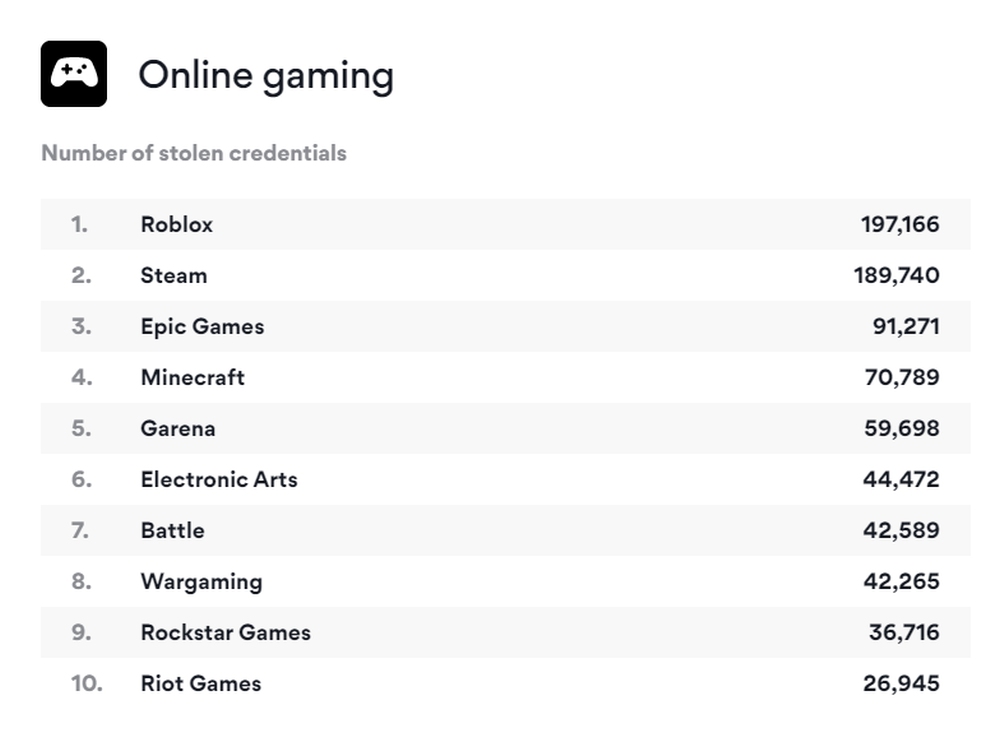
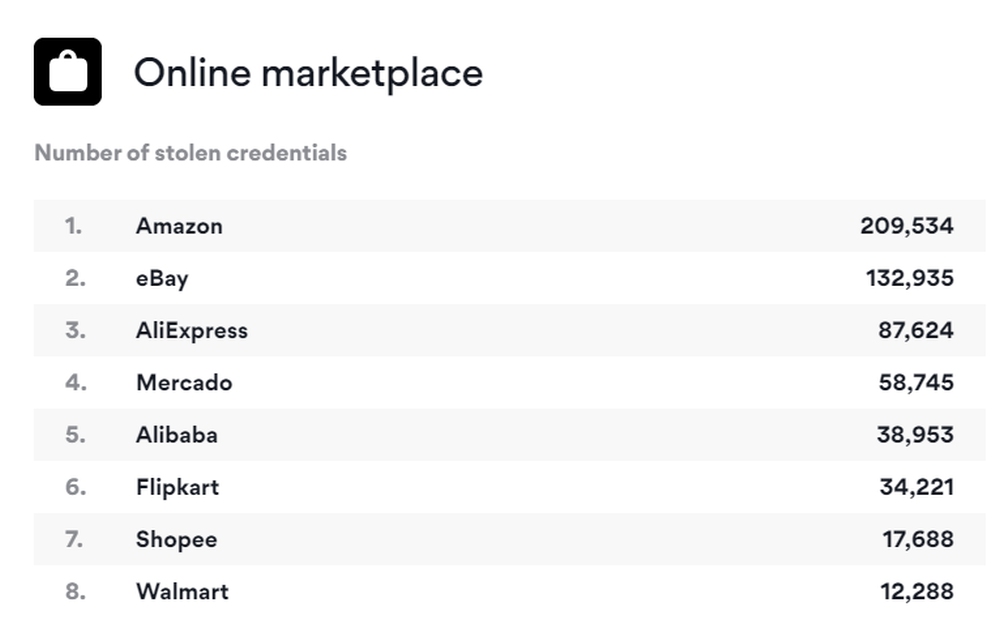
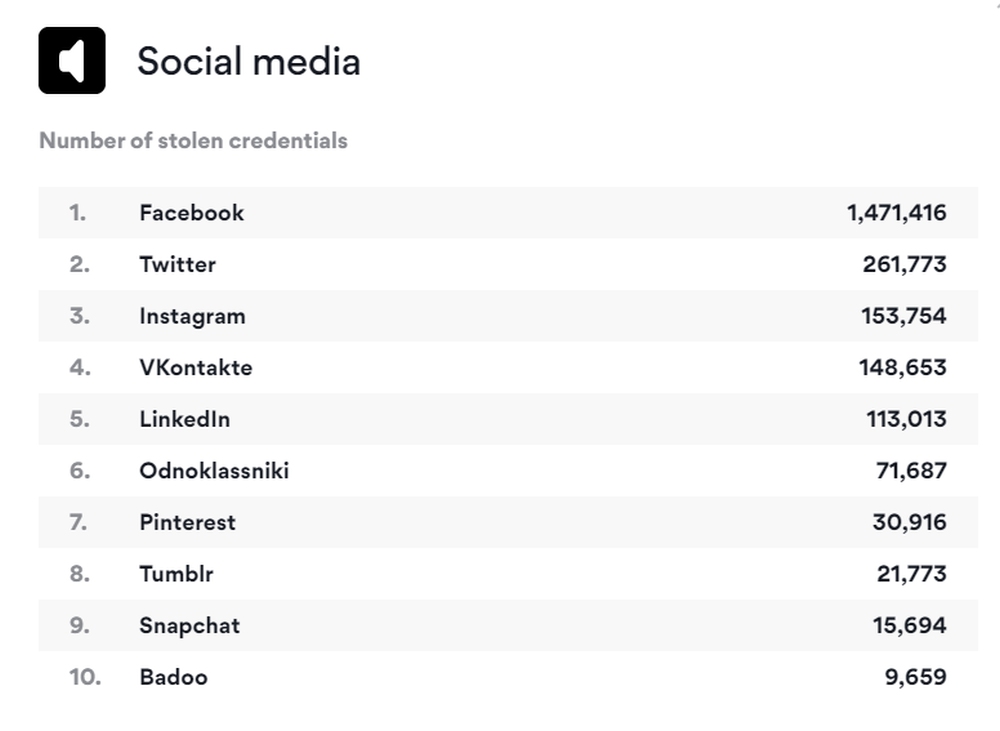
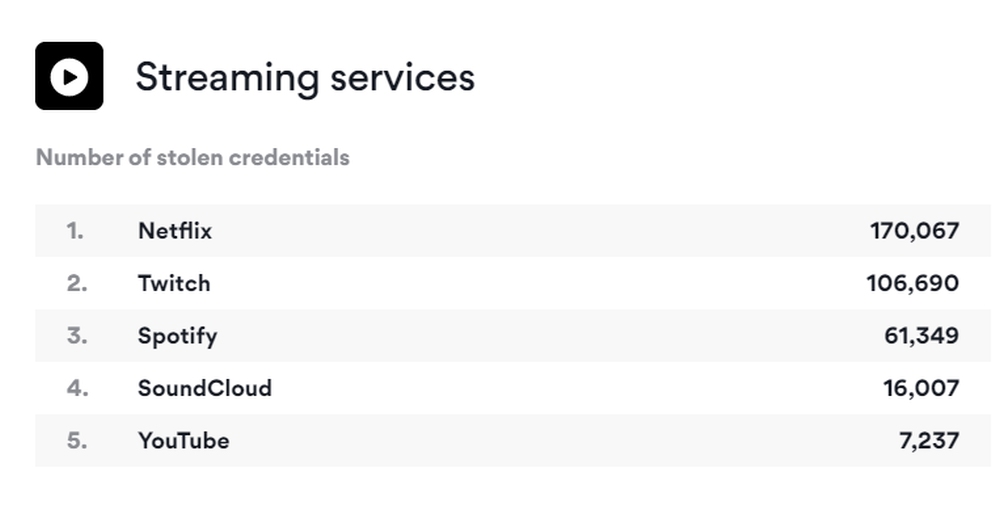
The compromised login information includes 1,471,416 Facebook credentials, 261,773 Twitter credentials, 145,436 PayPal credentials, 87,282 Dropbox credentials, and 1,540,650 Google account credentials. Other compromised accounts include (but aren’t limited to) Coinbase, Blockchain, Outlook, Skype, and Netflix.
Nordlocker also said that the virus “escaped with 6 million files” from Desktop and Downloads folders. They include 3 million text files, over 1 million image files, and 600,000+ Word files—as well as over 1,000 types of different files. The malware managed to photograph a user if the device had a webcam.
According to screenshots made by the malware, the virus spread through email and even illegal software like Adobe Photoshop, Windows cracking tools and pirated games. The malware itself was unnamed and likely a cheap, customisable variant that could have be purchased easily on the dark web.
“Nameless, or custom, trojans such as this are widely available online for as little as USD 100 (RM410). Their low profile often helps these viruses stay undetected and their creators unpunished,” wrote analysts.
However, Nordlocker stressed that they “did not purchase this database” or condone other parties doing it. They wrote that a hacker group “revealed the database location accidentally”.
How do you stay safe?
Hundreds of millions of passwords are compromised every year, and a lot of them can end up on the dark web. And the scary thing is that it might be impossible to tell if a file is infected—especially is the malware is new.
But Nordlocker also shared a few ways to stay safe, including using password managers to protect your credentials and auto-fill information, delete your cookies every month, only download software from the developer’s website and other well-known sources, and make sure that your antivirus is always updated. It is best to use different complicated passwords for each platform and enable multi-factor authentication.
[ SOURCE, IMAGE SOURCE ]