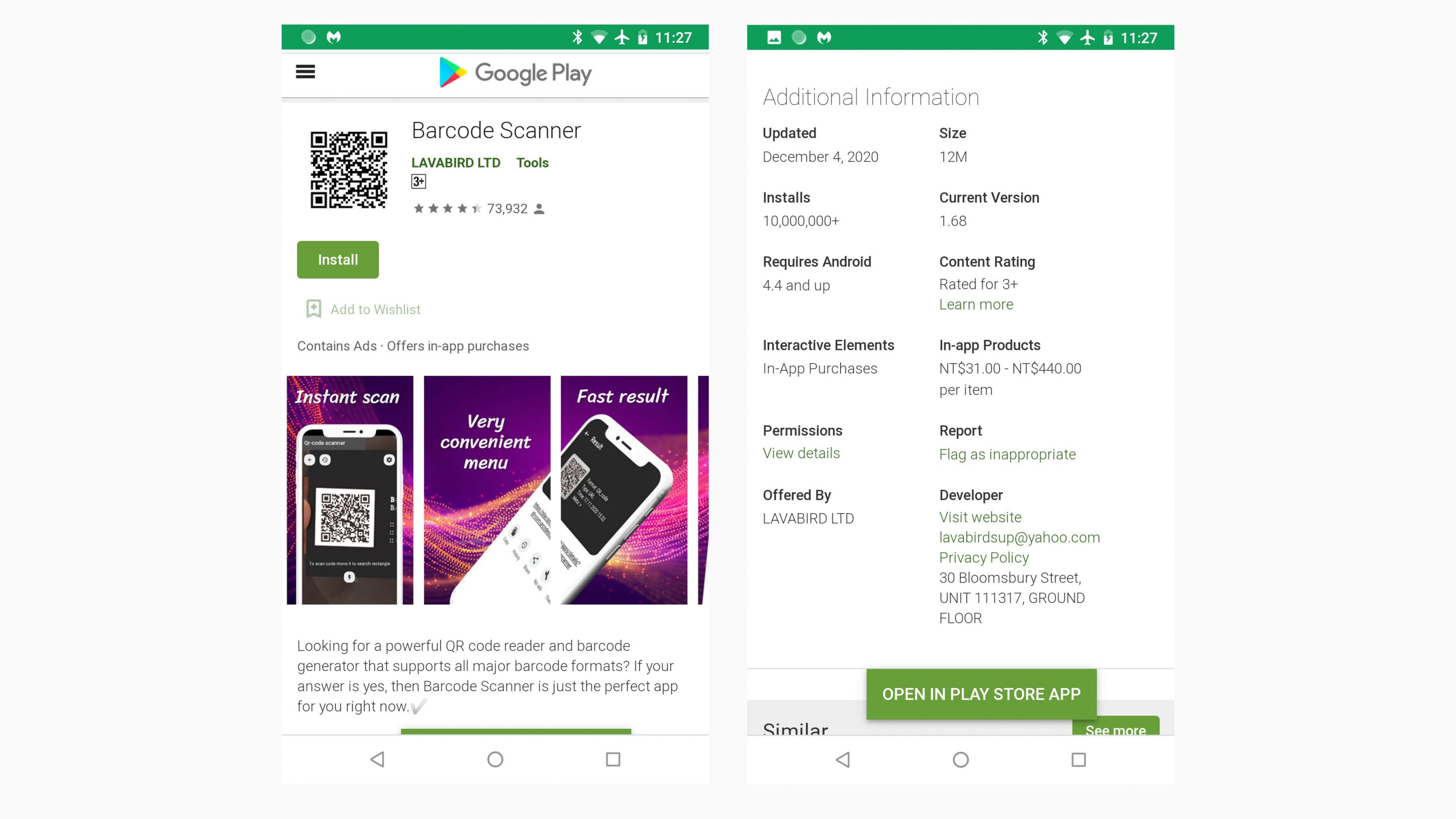
A popular QR code scanner on Google Play was transformed into a nasty bit of malware that has infected 10 million Android users. In a blog post, cybersecurity researchers at Malwarebytes reported that Android users who installed Lavabird Ltd’s Barcode Scanner app experienced adverts appearing unexpectedly on their Android devices.
The malware is said to open the default web browser by itself, without user interaction. Users are then directed to a dubious website that initiates a pop-up, compelling them to install an app called ‘Rocket Cleaner – System Optimizer’ that supposedly would improve the performance of their device.
It turns out that the QR code reader and barcode generator app has been on Goggle’s official app store for years. There is a good chance that users of the app downloaded it a long time ago and forgot about it.
Most new Android smartphone, including those by Samsung, have built-in QR code scanners with their camera app. All you need to do is launch your camera app, and it will scan a QR code.
According to Malwarebytes, a software update issued roughly on 4 December 2020, changed functions of the app to push advertising without warning. Researchers also said the malicious code was heavily concealed to avoid detection. In fact, the update was even signed with the same security certificate used in the past, clean versions of the Android app.
The report goes to say that the majority of free apps on Google Play include some form of in-app advertising. This is done by including an ad SDK to the code of the app. This is usually done at the end of an app’s development. In contrast, paid-for versions do not have this SDK.
In most cases, unwanted programs, ads and malvertising (an attack where perpetrators inject malicious code into legitimate online advertising networks) are connected with new app installations. But in this case, users reported that they did not install any new apps recently.
Malwarebytes explains:
Ad SDKs can come from various third-party companies and provide a source of revenue for the app developer. It’s a win-win situation for everyone
Users get a free app, while the app developers and the ad SDK developers get paid. But every once in a while, an ad SDK company can change something on their end and ads can start getting a bit aggressive.
Malwarebytes has reported its findings to Google and the search giant has removed the app from Google Play. But that doesn’t mean the app will disappear from infected devices. Users will need to manually uninstall the malicious app to be rid of it.
If you really need to install a QR code scanner app, here are some suggestions:
If you want to learn more about the infected app and how avoid it, go to Malwarebytes’ blog. You can also see a video that shows the malware in action.